The Data Security Platform for Enterprise
A single platform to discover, classify, and protect sensitive data and documents anywhere in your environment.



The DataStealth Data Security Platform (DSP) is a comprehensive suite of capabilities for your data security journey. Know where your data is, know what it is, and know that it’s protected through a holistic, end-to-end solution.
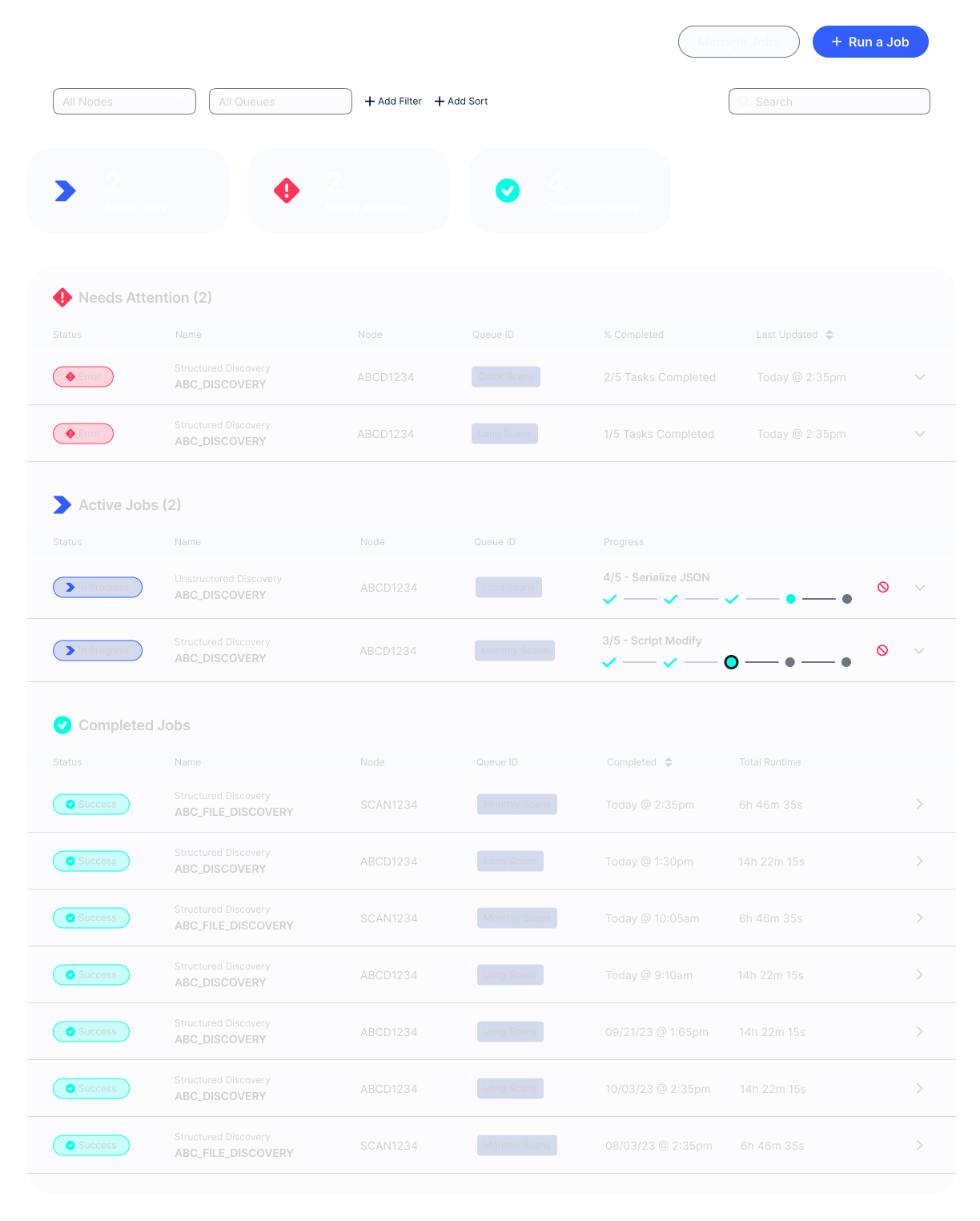
Discover known and unknown data sources, and structured and unstructured data, across your network.
Classify data with virtually no false positives to find what you're looking for with certainty.
Protect sensitive data using tokenization, encryption, or masking.
DataStealth is built for enterprise. With fast and easy integration that’s as simple as updating your DNS, you won’t need to make changes across every page of every application on every server.
Never required to make any application changes to be deployed.
Seamless deployment with no need to install agents, collectors, widgets on your servers or integrate with applications.
Transparent solution to users, systems, and processes.
We work with large enterprise customers in the banking, insurance, telco, and retail industries, allowing them to meet regulatory, governance, and compliance requirements with agility.

“DataStealth is an extremely flexible and robust solution that helps us locate and protect sensitive data in a wide variety of systems – from our legacy mainframes to our latest cloud-based apps.”
"The approach to securing sensitive data and preventing breaches that DataStealth uses is unlike any cybersecurity solution we have seen DataStealth is extremely innovative, powerful, flexible, and scalable – and is supported by their team’s deep technical expertise."

"It was a breath of fresh air to go from learning about DataStealth, to deploying the solution within 30 days."
Using core components of our Data Security Platform, DataStealth provides the solutions you need, all from a single platform.

Discover known and unknown sources, and classify data with virtually no false positives.

Intelligently mask any data in real-time, at the column and row level.

Protect any sensitive data in transit and at rest, not just PII and PHI.

Create high-fidelity test data to limit risk of exposure in non-production environments.

Reduce PCI audit scope by removing payment card data from your environment.

Comply with PCI 4.0's new requirements 6.4.3 and 11.6.1 by detecting and protecting payment page scripts.